Capture the Entire Self Checkout Scene
Introducing the CE-M10PA, the 10″ PVM designed explicitly for self-checkout theft deterrence.
Not just another 10″ PVM…
By utilizing corridor format on the built-in AXIS M3045 camera, the new portrait CE-M10PA captures a greater vertical field of view than traditional landscape PVMs. The increased vertical field-of-view allows the camera to capture the entire checkout process.
PORTRAIT ORIENTATION
Unlike traditional PVMs, the CE-M10PA features a portrait orientated LCD that showcases the entire view of the camera.

MOTION DETECTION
Built-In PIR Sensor triggers an optional flashing banner or LED light for increased security awareness.

CORRIDOR FORMAT CAMERA
Corridor format allows you to get a vertically oriented, “portrait” shaped video stream from the camera.

SECURITY BANNER
Choose from “Recording in Progress, Welcome, or Monitoring in Progress” security banners.
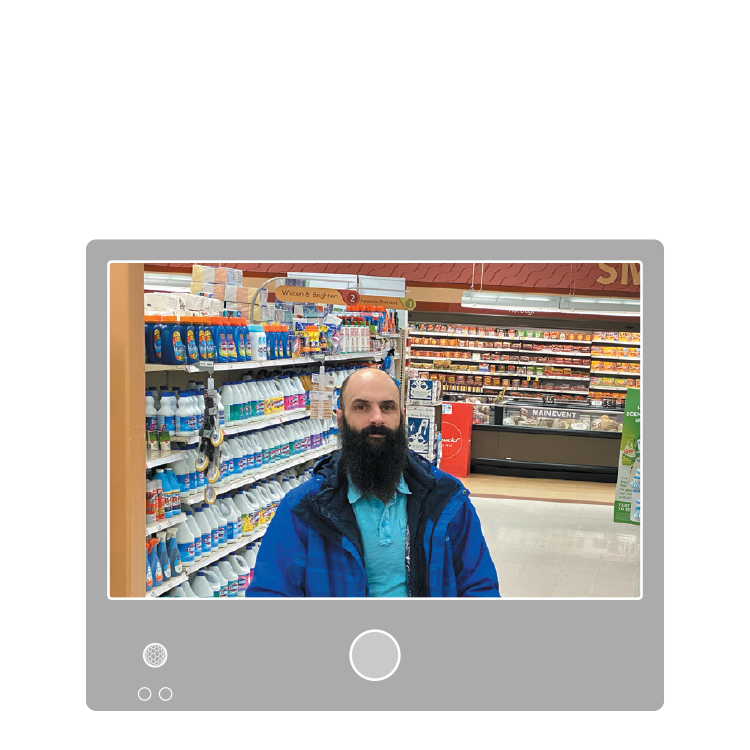
A Closer Look: Corridor Mode
In many surveillance situations, you want to monitor an area that is more vertical than horizontal in shape. This is particularly true for self-checkout installations, where the focus is on the entire checkout process. Take a look at the example below that compares a traditional PVM with the new CE-M10PA PVM.
Traditional PVM View
With traditional landscape format, the resulting image will have a 16:9 aspect ratio – perfect for monitoring entrances, exits, products, and wide aisles.
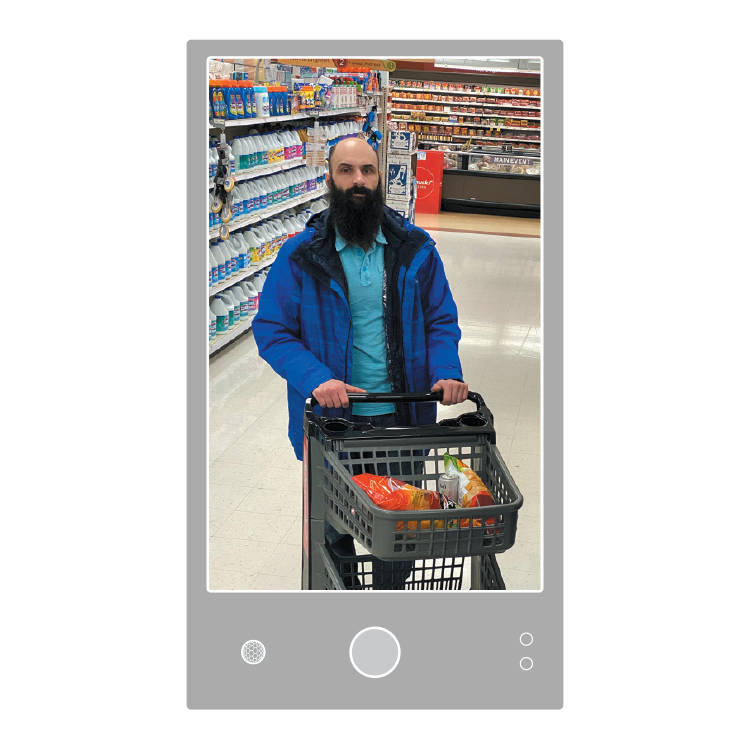
CE-M10PA PVM View
With Corridor format, the resulting image will have a 9:16 aspect ratio – perfect for monitoring self-checkouts, narrow corridors, hallways, and aisles.
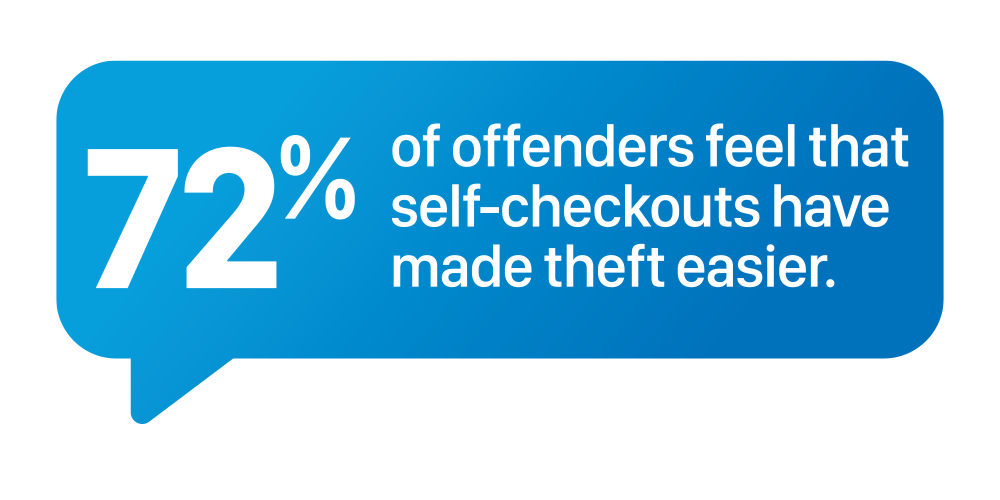
The Significance of Self Checkout PVMs
The seemingly simple self-checkout process presents many fraud-related vulnerabilities that impact the bottom line of retail businesses. PVMs can play an essential role in deterring self-checkout theft by creating security awareness.

Create Awareness
PVMs increase security awareness by informing the general public that video surveillance is in use, and their actions are recorded.

Deter Theft
Studies show that thieves are intimidated at the sight of a PVM and often leave the store immediately after noticing them.